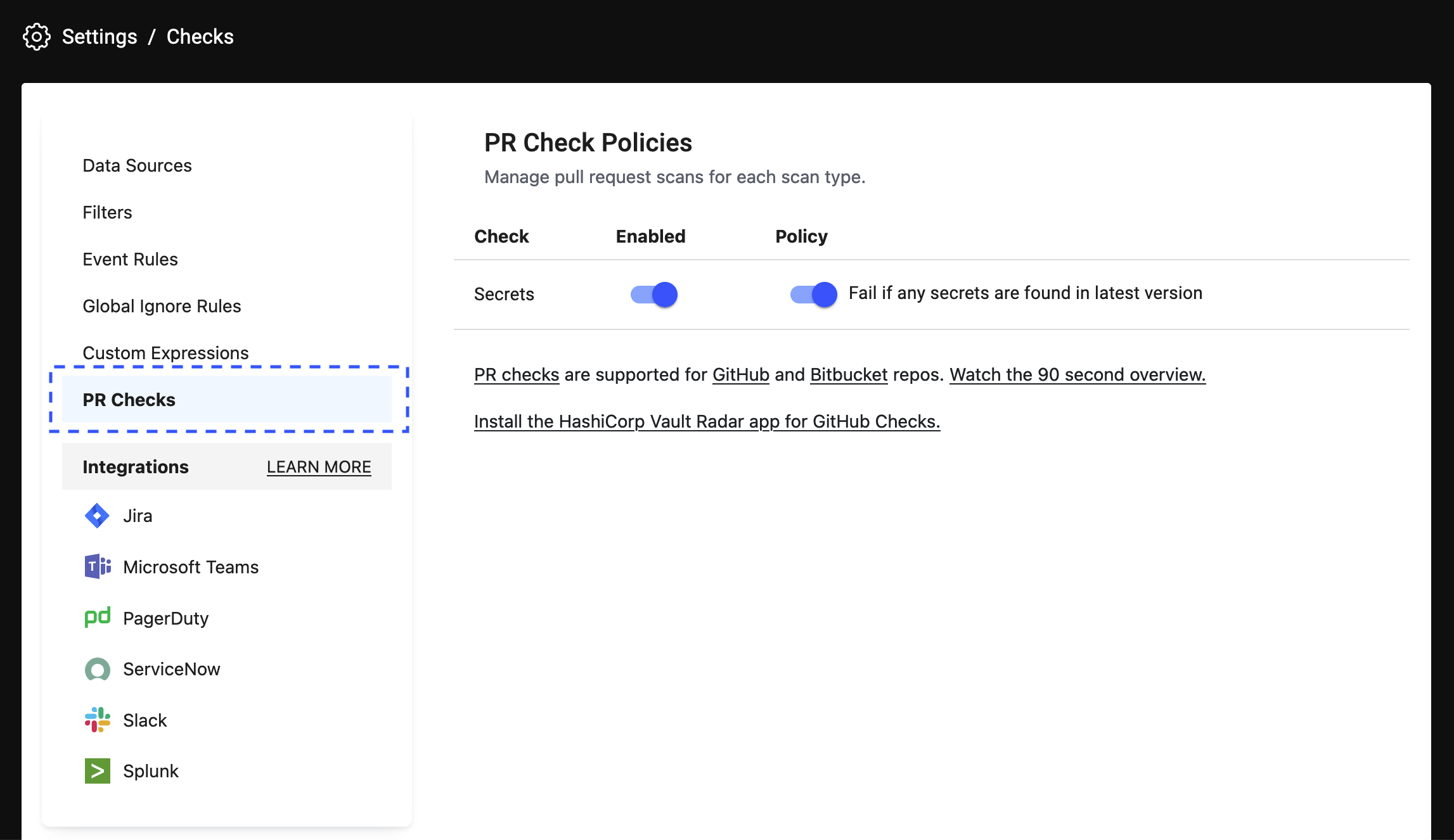
Pull request check policies
Pull request checks allow Vault Radar to perform a scan against a pull request for every pull request that is opened, and for every new commit to any open pull requests.
By default, the Vault Radar does not block any pull requests. Usage statistics show over 80% of warnings about secrets in PRs are fixed before commit, and the non-blocking workflow is more respectful of developer needs.
However, when appropriate, you can configure your data source provider provider to block the pull request from being merged if the check fails because sensitive data is discovered.
Vault Radar will alert you to any sensitive data found in the pull request, including both the tip of the pull request and the history of any commits. The alert includes details on where and what type of secret was found.
GitHub Checks
To enable pull request checks on GitHub, an Vault Radar application must be installed.
Note
Personal organizations are not currently supported with the checks workflow.
Prerequisites
- Vault Radar project is configured and resources monitored
- To install the Vault Radar app for GitHub Checks, permissions to install a GitHub App on an org are required. This would be an organization owner or someone with admin level permissions in a repository.
- The organization you are monitoring is not a personal org.
GitHub Cloud
Vault Radar accounts are monitored by the Vault Radar Checks App.
- Install the Vault Radar Checks App. (this must be done by someone who has permissions in GitHub to install the app).
Once installed, your future PRs and commits to PRs in monitored repos will be checked by Vault Radar.
GitHub Enterprise Server
This version of GitHub Checks is for customers using the self-managed GitHub Enterprise Server.
Create the GitHub Enterprise Server Checks app following the instructions here. Note that a step in those instructions is to send the configuration details to the customer success team. Wait for confirmation from the team before proceeding.
Install the app created from step 1 on the organization (this must be done by someone who has permissions in GitHub to install the app).
Once installed, your future PRs + commits to PRs in monitored repos will be checked by Vault Radar.
Configure repositories
To configure which repositories the Vault Radar app for GitHub Checks monitors after installation:
Go to your GitHub organization → settings → GitHub apps (the URL pattern is
github.com/organizations/{orgname}/settings/installations) to review all applications installed in the org.Find the Vault Radar app for GitHub Checks in the list and click the configure button.
Using the GitHub interface, make selections about which repos the app can access, and save the changes.
Any changes take effect with the next pull request (or commit in an open pull request), and apply to all users of the org.
Disable GitHub checks
Follow the steps to configure the Vault Radar GitHub Checks app.
From the configuration page, select either suspend or uninstall.
Both options take effect immediately and apply to the entire GitHub org.
Bitbucket Insights
To turn on pull request scans on Bitbucket:
Navigate to your Bitbucket repo, and click on any commit. Within that commit view, in the bottom right hand corner there should be an option to index your repo by clicking Go to pull request. This may take a few minutes while the repository gets indexed in the background.
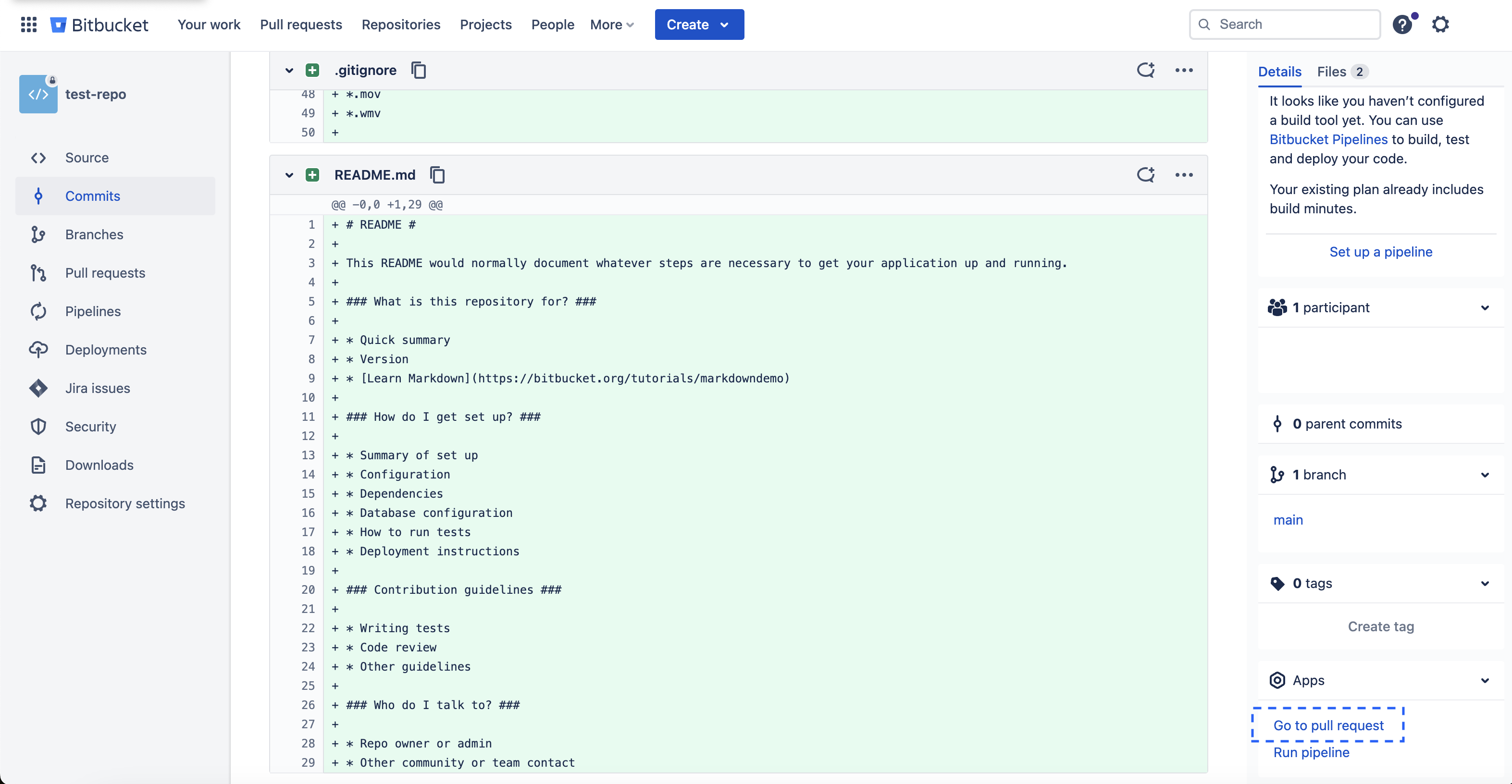
Contact the customer success team to enable Bitbucket Code Insights in your project.
Once set up, your future PRs and commits to PRs in monitored repos will be checked by Vault Radar and results will be uploaded to the Reports section of your pull request.